It’s nothing new. Confidential information, sensitive financial records, critical customer data, and intellectual property are core assets for any successful business. Protection of these assets is critical to the longevity of any successful business.
Theft of these assets have long provided the motivation to individuals and competitors to go off-script to indulge in nefarious acts or even high-profile criminal espionage schemes. Actions taken are often unseen and resulting impacts not realized until the damage has been done. These actions are not evident due to the covert nature of the acts being taken.
It seems everyone may want a slice of YOUR pie. Maybe they think it is easier to take it away than earn it. Or maybe they don’t think it is yours to begin with. But no matter who it is, no matter the reason they are after your information, no matter how they plan to get it, in the end, it can be a costly loss for your business.
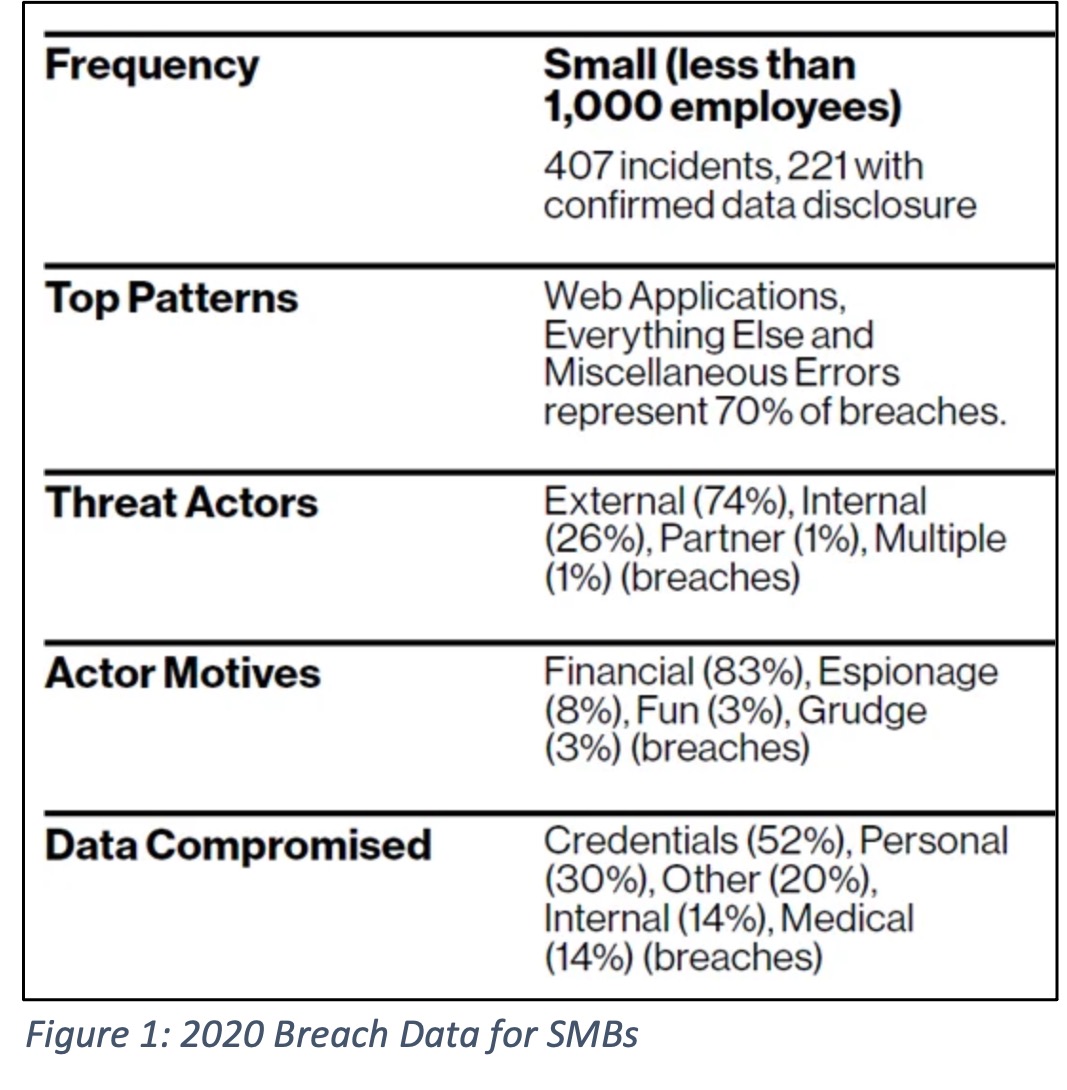
When faced with mitigating the risks to private company information, many businesses focus on the obvious…build a barrier! Keep the bad guys out and don’t let them near our stuff. And while 74% of all data breaches come from outside attacks, it is the 26% of insider threats that often go unchallenged. No one wants to think they could be at risk from the inside. No way…our team is loyal to the core and would never do anything malicious to jeopardize our success. But do not be so sure.
It is critical to note: No one said it has to be intentional? Insider threats come from a wide range of sources, intended or otherwise. Let’s take a closer look at three major threat groups:
The Naive Insider – This culprit could be a young associate looking for quick ways to climb the corporate ladder. They dig through volumes of company data in search of that one thing that they can use to propel them into the “Employee of the Month” spotlight. Unfortunately, in their search, they tend to look at policies and procedures as impediments to their goal. So, accessing, sharing, posting, or repurposing sensitive data is fair game. These actors are the hardest to spot. Their intentions are pure, their dedication to the company is solid, but their methods could put companies at unnecessary risk.
The Negligent Insider – Being naive sure seems innocent, but when it comes to negligent threats, innocence is not in play. Negligent insiders are often at the top of the organizational chart. They are Executives, VPs, or any other employee who simply feels no need to conform to the security practices in place to protect the company. They are “too busy”, and their time is “too valuable” to change their password every 90 days. They need to use a thumb drive to move files around because it is too much of a burden to post them to the well-protected file server or cloud drive. In fact, they may try and make a case that a thumb drive is far more secure than sharing data to the cloud. No matter their rationale for bypassing security policies and practices, their negligence is a ticking time bomb. And when the explosion happens, the most sensitive information gets taken.
The Criminal (or intentionally malicious) Insider – These are the threat that makes the crime movies so exciting. Malicious pawns are focused and intent on causing great loss to your company. These actors come in two flavors…the obvious are the ones that infiltrate your inner circle of employees for the sole purpose of stealing your data and intellectual property right out from under your nose. Rare, but they do exist. The other, more prevalent type of criminal insiders is the disgruntled employee. These no-gooders can be overheard mumbling “I’ll show you!” as they hustle back to their computer, log in, and set their sights on showing you who is boss. These threats are a bit easier to observe and manage if you have good communication within your company, but without proper protections in place, the misuse of their credentials could wreak havoc on your business. Think of the angry salesperson who decides to take all your customer data that you have spent years or decades collecting. Or your jilted network administrator who goes through the paces to test all the backdoor access holes they set up years ago.
None of these threat groups may come as a surprise. In fact, written down they seem obvious. Understanding these facts is good, but what is your company doing to proactively guard against these risks? Is company data and intellectual property moving across several platforms (internal network, VPN, Cloud, vendor portals, etc.)? If so, it can be hard to have eyes on it all.
The good news is that there are a number of affordable methods and solutions JETT Business Technology can help you with. After we assess what options are best for your company and employees, we tailor a plan specific to your risk mitigation needs and your budget. Whether the best option is endpoint monitoring, user behavior analytics, enhanced privileged account management, a combination of each, or something as simple as a training and awareness refresher program, we can help. But no matter what you take away from this, remember…no threat, malicious or otherwise, can be stopped if it is not seen.
Contact JETT Business Technology and someone will reach out to you to discuss your needs. We can share more about our entire suite of security solutions that mitigate insider threats, external threats, targeted phishing attacks, ransomware threats, as well as our lunch-and-learn employee awareness programs.